Insider Threat Program Template
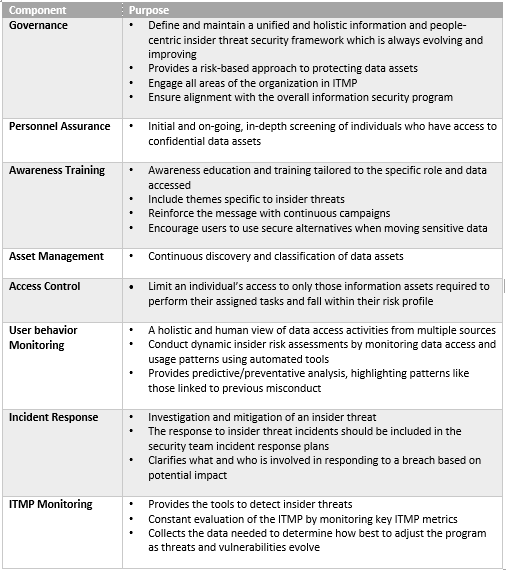
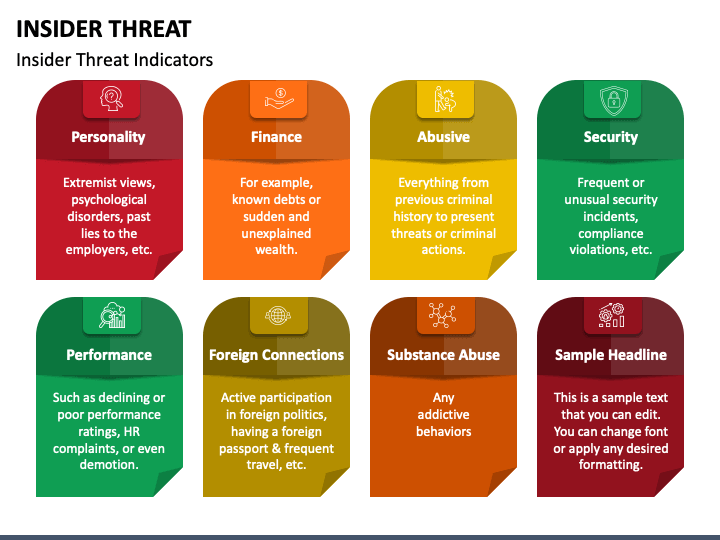
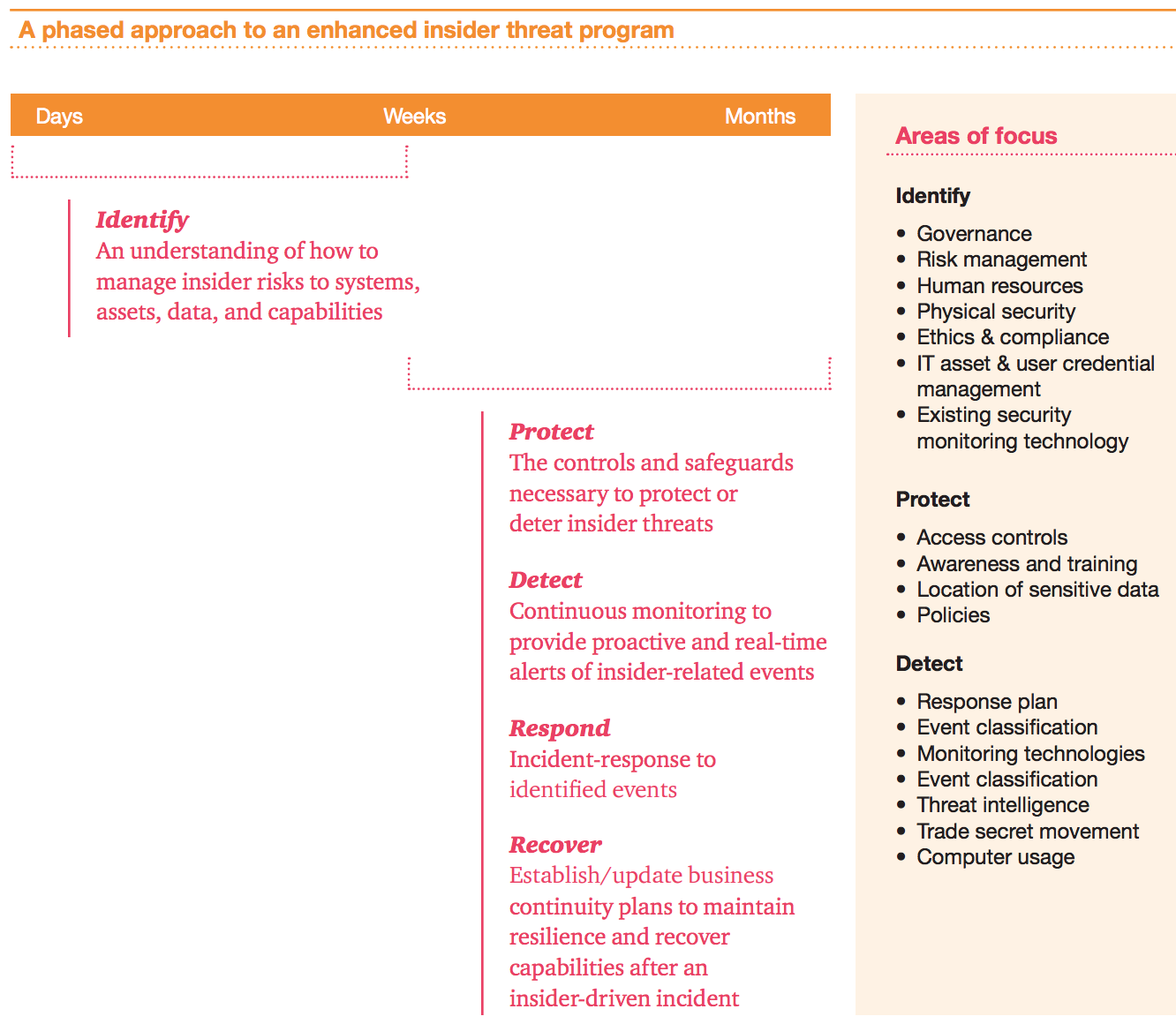
Insider Threat Program Template - This plan establishes policy and assigns responsibilities for the insider threat program (itp). Establish a formal program for identifying, mitigating, and responding to insider threats, including clear reporting mechanisms. Develop an insider threat program: Dod insider threat program template. An insider threat is any risk to your organization that arises from an internal party’s access to your systems, assets, or data. The cybersecurity and infrastructure security agency (cisa) created these reporting templates as a tool for stakeholder organizations to download, review, and. Once an organization has developed an insider threat program plan, it is essential to implement the plan and regularly review and update it. Easily downloadable as an ms word file, helps you establish effective insider threat strategies in compliance with dod guidelines. Nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. As an example of an insider threat, in 2024,. Mplementing an insider threat management program (itmp). There are countless statistics about cybercrime and one of the most impactful is that for threat actors. Their profits continue to increase year over year and are on track to rise from. Easily downloadable as an ms word file. It also describes the differences between an inquiry and an investigation. The itp will seek to establish a secure. Nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. This plan establishes policy and assigns responsibilities for the insider threat program (itp). This guide supersedes the previous insider threat program guides issued by the nittf and ncsc including the nittf’s 2014 “guide to accompany the national insider threat policy and. The cybersecurity and infrastructure security agency (cisa) created these reporting templates as a tool for stakeholder organizations to download, review, and. The itp will seek to establish a secure. Develop an insider threat program: Establish a formal program for identifying, mitigating, and responding to insider threats, including clear reporting mechanisms. Insider risk is the potential for an individual with access to an organization’s data resources to intentionally or accidentally perform an activity that negatively impacts the. An insider threat is any. The itp will seek to establish a secure. This plan establishes policy and assigns responsibilities for the insider threat program (itp). The itp will establish a secure operating environment for personnel, facilities, information,. Establish a formal program for identifying, mitigating, and responding to insider threats, including clear reporting mechanisms. Please click on the nittf technical page to review these bulletins. This job aid explains how insider threat inquiries function within insider threat program operations. Easily downloadable as an ms word file, helps you establish effective insider threat strategies in compliance with dod guidelines. To establish and maintain an insider threat program to detect, deter and mitigate insider threats. The itp will establish a secure operating environment for personnel, facilities, information,.. Insider threat to deter employees from becoming insider threats; Dod insider threat program template. Detecting insiders who pose a risk to classified information; As an example of an insider threat, in 2024,. Customizable insider threat program template, designed for federal contractors and local, state, and federal agencies. The program must gather, integrate, and report relevant and credible information covered by. Easily downloadable as an ms word file, helps you establish effective insider threat strategies in compliance with dod guidelines. This plan establishes policy and assigns responsibilities for the insider threat program (itp). Insider threat to deter employees from becoming insider threats; There are countless statistics about cybercrime. Easily downloadable as an ms word file. Mplementing an insider threat management program (itmp). Nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. Dod insider threat program template. Detecting insiders who pose a risk to classified information; Mplementing an insider threat management program (itmp). Insider threat to deter employees from becoming insider threats; Nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. Please click on the nittf technical page to review these bulletins. Their profits continue to increase year over year and are on track to rise from. Their profits continue to increase year over year and are on track to rise from. As an example of an insider threat, in 2024,. And mitigating the risk of an insider threat. The cybersecurity and infrastructure security agency (cisa) created these reporting templates as a tool for stakeholder organizations to download, review, and. This guide supersedes the previous insider threat. Easily downloadable as an ms word file, helps you establish effective insider threat strategies in compliance with dod guidelines. Customizable insider threat program template, designed for federal contractors and local, state, and federal agencies. Nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. The itp will seek to establish a secure. Once an. Please click on the nittf technical page to review these bulletins. The cybersecurity and infrastructure security agency (cisa) created these reporting templates as a tool for stakeholder organizations to download, review, and. This job aid explains how insider threat inquiries function within insider threat program operations. Insider threat to deter employees from becoming insider threats; Easily downloadable as an ms. Easily downloadable as an ms word file. Insider threat to deter employees from becoming insider threats; Establish a formal program for identifying, mitigating, and responding to insider threats, including clear reporting mechanisms. The itp will seek to establish a secure. And mitigating the risk of an insider threat. There are countless statistics about cybercrime and one of the most impactful is that for threat actors. The cybersecurity and infrastructure security agency (cisa) created these reporting templates as a tool for stakeholder organizations to download, review, and. Mplementing an insider threat management program (itmp). Please click on the nittf technical page to review these bulletins. Insiders can damage your company in countless ways, from destroying valuable equipment, to leaking sensitive data, to providing access to unauthorized third parties. Their profits continue to increase year over year and are on track to rise from. An insider threat is any risk to your organization that arises from an internal party’s access to your systems, assets, or data. Nittf has developed technical bulletins that identify key technical issues in developing an insider threat program. The itp will establish a secure operating environment for personnel, facilities, information,. The program must gather, integrate, and report relevant and credible information covered by. This job aid explains how insider threat inquiries function within insider threat program operations.Insider Threat Program Template
Insider Threat Policy Template
Insider Threat Program Template
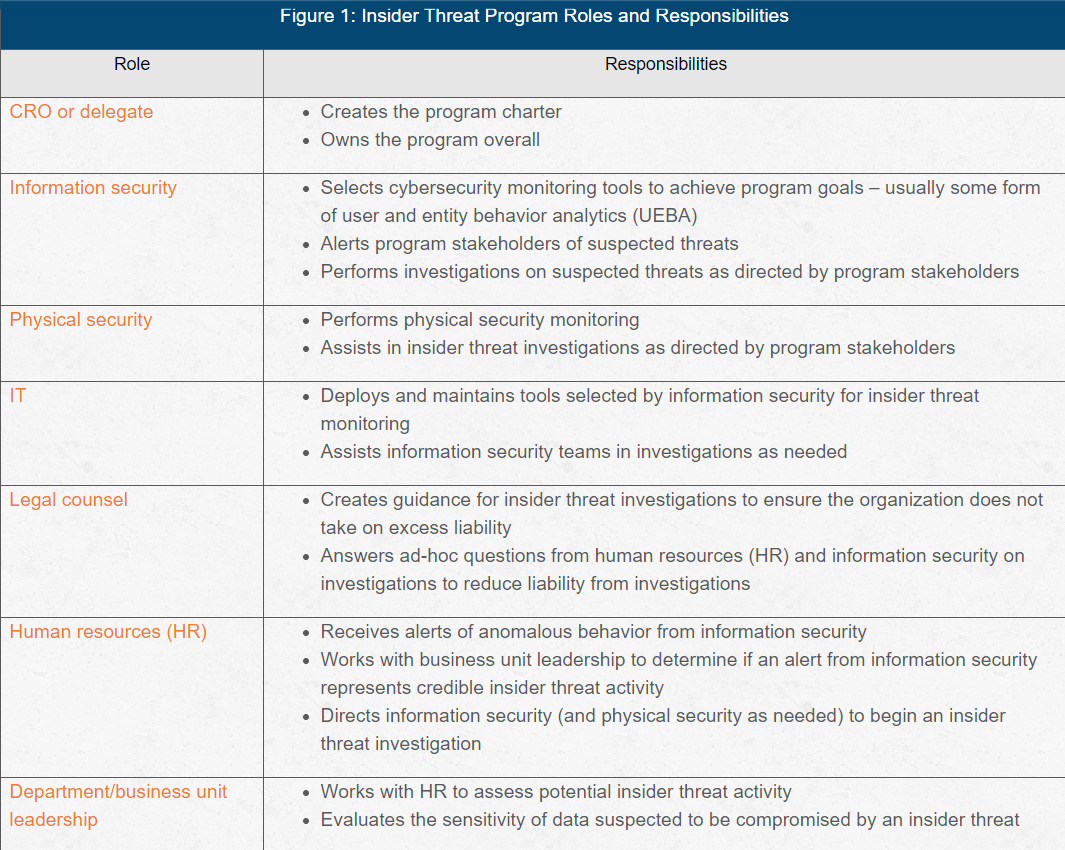
How to Establish an Effective Insider Threat Program
Insider Threat Program Template
Insider Threat Program Template
Insider Threat Program Template
Insider Threat Plan Template
Insider Threat Program Template
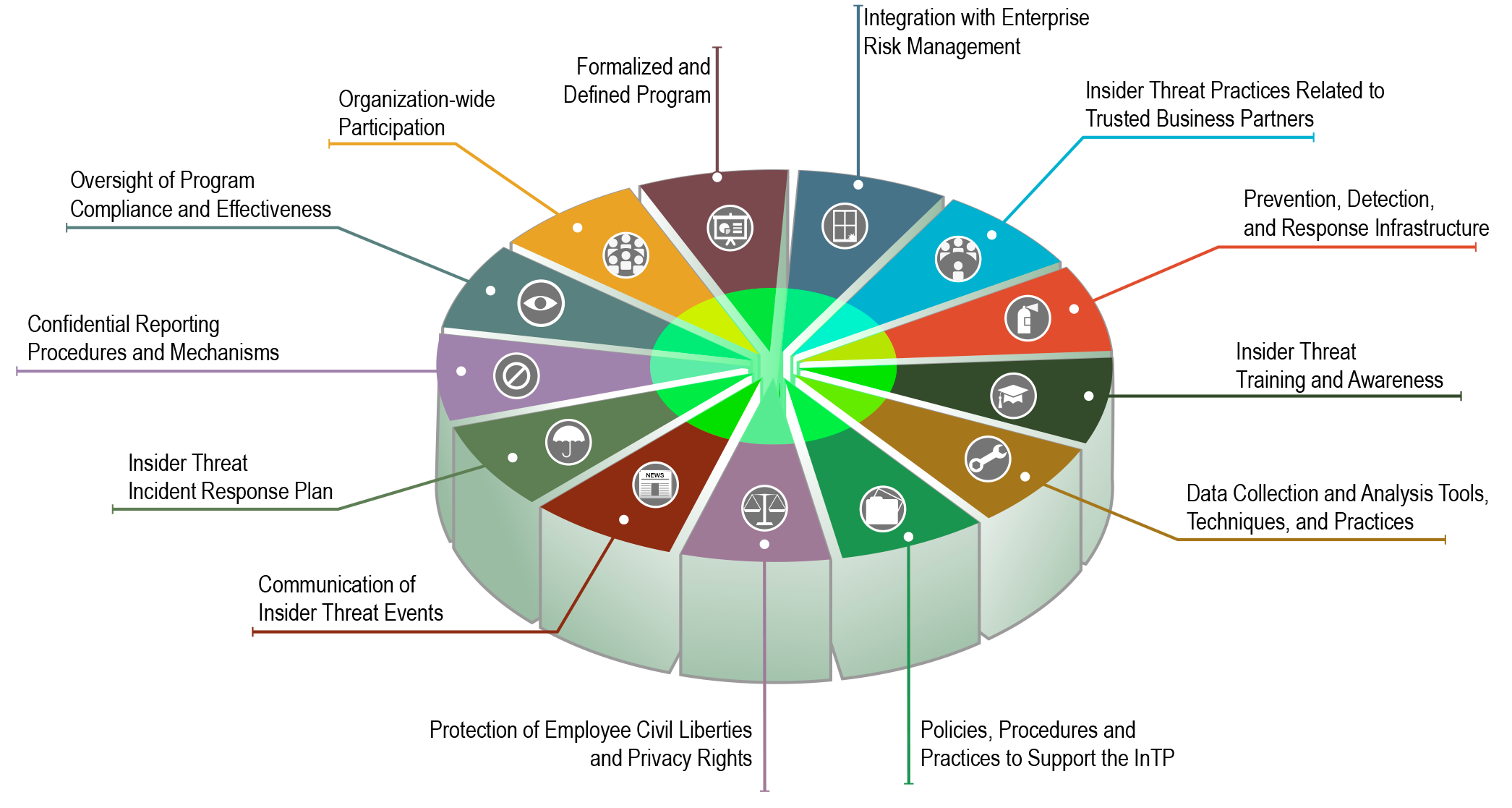
Establishing a Foundation and Building an Insider Threat Program
Insider Risk Is The Potential For An Individual With Access To An Organization’s Data Resources To Intentionally Or Accidentally Perform An Activity That Negatively Impacts The.
It Also Describes The Differences Between An Inquiry And An Investigation.
Customizable Insider Threat Program Template, Designed For Federal Contractors And Local, State, And Federal Agencies.
Once An Organization Has Developed An Insider Threat Program Plan, It Is Essential To Implement The Plan And Regularly Review And Update It.
Related Post: